You Have No Idea How Insecure Your iPhone Is
iPhone security is an all-time concern for users. Though iPhone is exactly famous for its security system, it doesn't mean that there is no way to access your privacy in your iPhone like photos, videos, messages, call history and conversations on social apps like Facebook, Instagram, Snapchat, WhatsApp and so on. Actually, according to a survey, over 80% iPhone are actually insecure. So, you should protect your iPhone with enhanced security, let's see how to make your iPhone invincible.
Don't Miss Out:
- Do You Know? 8 iPhone Settings Upgraded in iOS 11
- Apple ID is Disabled? This is A Time & Money Saving Guide for You
CONTENTS
Attach Great Importance to Screen Lock
Limit the Usage of Third-Party Applications
Never Let Others Know Your Location
Don't Use Auto-Fill in Safari or Other
Enable More Security Settings
Attach Great Importance to Screen Lock
1. Set A Unfathomable Passcode
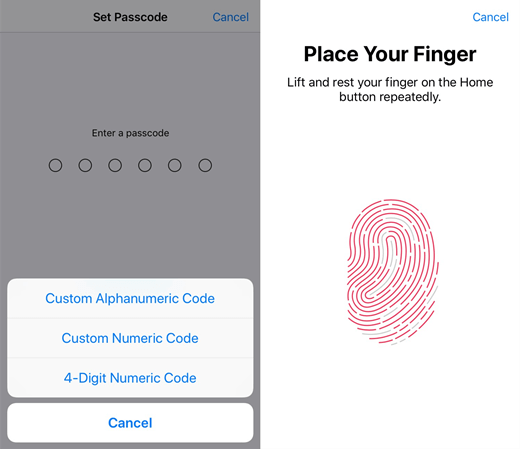
Many like to set a passcode with pure numbers or letters. People with an awareness of iPhone security will combine a passcode with both numbers and letters. Also, don't use "4-Digit Numeric Code" but instead opt to "Custom Alphanumeric Code" or "Custom Numeric Code".
2. Enable Touch ID and Face ID
Touch ID is a highly strong way of security protection. Users will have to record their fingers or ringers of reliable people at first, and then only people with authentic fingers will be able to access the iPhone. Moreover, it's recommended to record at least two fingers of yours in case that one of them gets injured and fails to pass the authentication.
Apple has been devoting to the iPhone security and attaching great importance to user privacy. iPhone X has brought a new security protection system for us, say, Face ID, which uses advanced technologies to accurately map the geometry of your face. With a simple glance, Face ID securely unlocks iPhone X.
3. Limit Accessibility When Locked
Even when the screen is locked, some apps are still allowed to access your iPhone. Years ago, there was a bug that malicious people can send messages or make calls on a locked iPhone and that somehow makes the screen lock disabled.
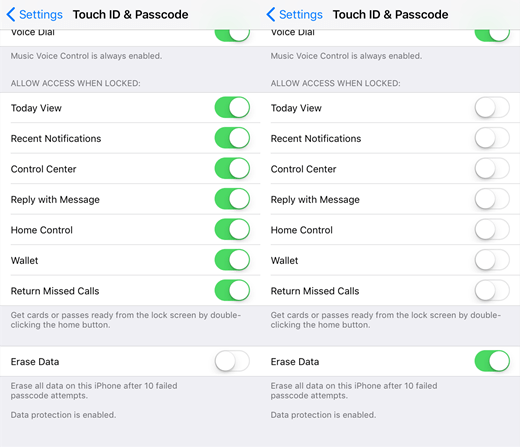
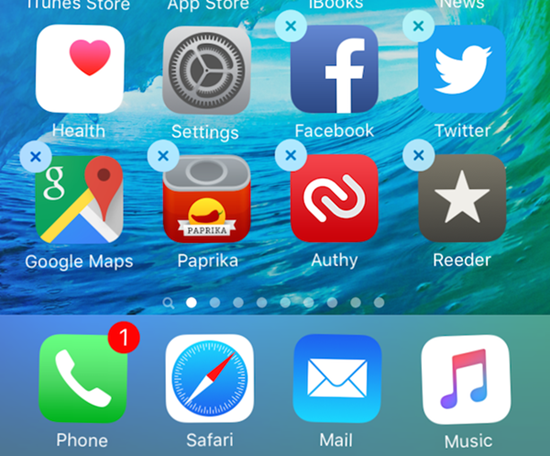
By default, quite a lot of apps are still able to launch when locked, including Wallet, Today View, Control Center, Home Control, Reply with Message, Return Missed Calls, Recent Notifications. I'd suggest you to turn off most of them in "Settings" > "Touch ID & Passcode" > "ALLOW ACCESS WHEN LOCKED".
4. Erase Data to Protect Privacy
If your iPhone got lost or stolen, the big question of your concern is whether your private data would be leaked. Data now even outweigh money a lot. To dismiss such a misgiving, I'd recommend you to enable the "Erase Data" feature in "Settings" > "Touch ID & Passcode".
The "Erase Data" feature will erase all data on this iPhone after 10 failed passcode attempts as a way of data protection. This is an unwanted situation for certain. To avoid data loss, you should regularly back up your iPhone with iTunes or iCloud.
Limit the Usage of Third-Party Applications
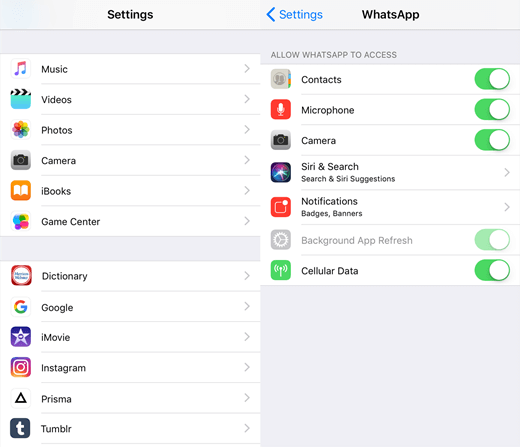
When we open the apps that are done installing on iPhone for the first time, many notifications will pop up asking us whether to allow this and that, like allowing to access camera, photos, contacts, locations, and so on. Most people may think that's not a big deal to allow things of these kinds.
However, that's the beginning of leaks of privacy in most cases. Certainly, it's okay to allow apps downloaded from App Store to access other apps, for these apps are downloaded from authentic sources. However, if the app is not from a reliable source, you should be careful about it.
If you don't know how to change the authorizations for apps to access others, it's actually a cinch. Open the "Settings" and swipe down to apps. Then, select your desired ones and change the settings. You should pay attention to those apps that are allowed to access your contacts, camera, photos, location, and wallet.
Never Let Others Know Your Location
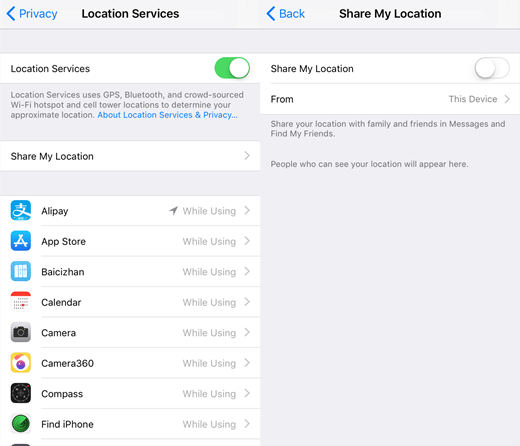
I believe most people possibly pay the least attention to the location services. However, location privacy is also something that you should care about, especially if you have a sensitive girlfriend or boyfriend. Now, let's take care of location services on your iPhone.
1. Stop Sharing Your Location
It would be good for others to keep up to date with your location when you're traveling outside. However, you should turn it off when unnecessary. Open the "Settings" app and go to "Privacy". Click "Location Services" and select "Share My Location". Now, toggle it off.
2. Limit Ad Tracking
Do you know the Ad tracking is actually using your location information as well? As to analyze your personal hobby and send ads targeted to your interests, Ad Tracking will be able to access quite a lot of your privacy when on. Therefore, I'd recommend you to keep it off. Go to "Settings" and choose "Privacy". After that, swipe to the bottom and select "Advertising" and toggle on "Limit Ad Tracking".
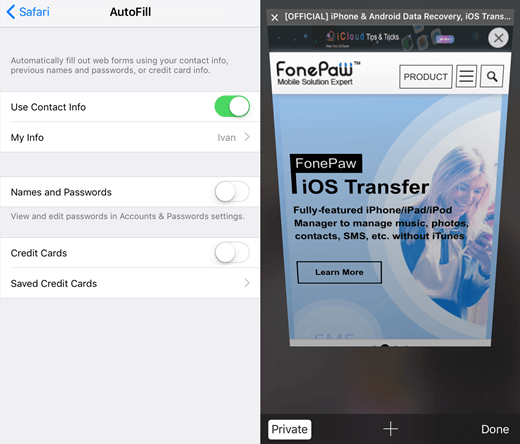
Don't Use Auto-Fill in Safari or Other
If you spend quite a lot of time surfing the internet with your iPhone, the Auto-Fill feature must be useful. However, I don't think it's a good one when it comes to iPhone security, though I think this can save plenty of troubles. However, since the usernames and passwords are all kept in a place and easy to access, it's easy for others to reach your privacy as well.
If you want to prevent others from seeing your activities on Safari or other browsers, it's a good idea to use the Private mode, which opens an incognito window that nobody can track.
Enable More Security Settings
1. Enable Two-Factor Authentication
To apply an extra layer for iPhone security, it's strongly recommended to use Two-Factor Authentication, which use your trusted devices and phone numbers to verify your identity when your Apple ID is signing in another device or other sites. Here is a full introduction to Two-Factor Authentication. You might as well take a look and see how to enable the authentication.
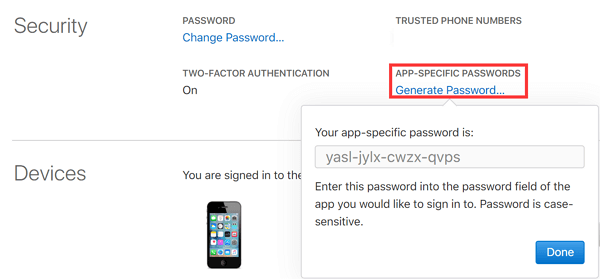
2. Use App-Specific Passwords
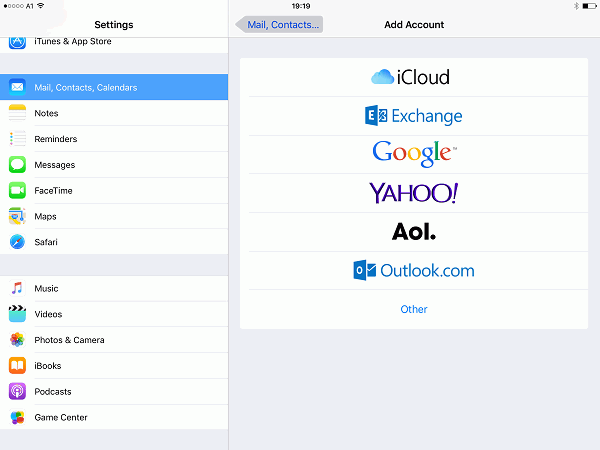
You can try App-specific passwords, which allows you to sign in to your account securely when it comes to using your Apple ID in other third-party apps like Microsoft Outlook, Mozilla Thunderbird, or other mail, contacts, and calendar services not provided by Apple.
App-specific passwords are single-use passwords for your Apple ID that won't be collected or stored by any third-party apps you use. If you want to generate an app-specific password, you should have enabled Two-Factor Authentication at first. Then, sign in the Apple ID account page and go to the "Security" section. Click "Generate Password" and enter a password label. After that, click "Create" and a password will be produced.
If you've already done all the above on your iPhone, there is no one who can hack and access your private data. Hope you enjoy this essay. If you like it, why don't you share this article with your friends?
Advance Notice: Do you like Live Photos on your iPhone, if you want to make the most of it, you certainly would not like to miss the upcoming article.





















A lot of people are looking for genuine hacker .I'm recommending Charliehacktivist@ gmailcom this team are good when it comes to hacking and they are also a private investigator who can help u find it about your unfaithful partner . Contact them now and be free fro lies and deceits.
HI everyone,HONESTLY I also gave up before i was able to hack my partner's whatsapp messages remotely and gained access to all the chat and calls with the help of LORDGIFTSPY AT GMAIL com,She is reliable and very fast.i use her Whenever I want to be sure about someone,if you require her services tell her I referred you.
•Reply•Share ›
Never worry about hacking.contact HACKERJOSH03 AT TWEETER and contact him on GM AT HACKERJOSH911 .he is cool
never be disturbed about unlocking ur iphones and getting te password to a social media account without anyone knowing.contact HACKERJOSH911 AT GMAIL AND TWEETER AT HACKERJOSH03
sure HACKERJOSH911 AT GMAIL AND TWEETER AT HACKERJOSH03.he is the greatest in this job
hello you need any hacker to help you in any hacking device kindly connect to us at our team via mail snakehacker2 at gmail .com
Since I have met (HACKSPYIEZ@gmail) I have no problems on any hacking issues thank you HACKSPYIEZ @ Gmail for the best job I'm also using this medium to recommend her to everyone on any issues...
never be disturbed about unlocking ur iphones and getting te password to a social media account without anyone knowing.contact HACKERTOM10 AT GMAIL
Hi,at a point,I was about loosing my home ,I got in contact with LADYPAMY15 AT GMALE ,and she helped me that my wife has been going out with another man,you can also contact her .
Hi,at a point,I was about loosing my home ,I got in contact with hackerscott211@gmail. Com ,and he helped me that my wife has been going out with another man,you can also contact him. Hackerscott211
Never worry about hacking.contact hackerscott211@gmil. Com AT TWEETER and contact him on hackerscott211@gmail. Com .he is cool
I recommend [email protected] for help and any information you need
Contact [email protected] for help or any information
I will advice you to contact [email protected] for help
HACKDON005 is a Team Of Professional HACKERS , a product of the coming together of Legit Hackers from the Dark-Web (pentaguard, CyberBerkut, White Hack and Black Hat,) whose system is a very strong and decentralized command structure.
I will advice you to contact [email protected] for help
HACKERSUSAN78 AT GEE MAIL. COM WILL HELP YOU OUT
Contact [email protected] I recommended him