The Top 7 Mobile Phone Security Risks You Need to Know About – and What You Can Do About Them
Your mobile phone probably plays a fairly essential role in your life – the vast majority of people today use their mobile device for almost every aspect of their lives: as a source of entertainment, a practical way of managing everyday tasks, a device to browse and shop on, and even as a form of personal identification or to make payments. With so much tied up with a single device, the data they hold is immensely valuable and can pose an enormous risk if it’s accessed without permission. In this article, we take a look at some of the major security risks involved with mobile phones and suggest ways that you can tackle them.
Be wary of third-party mobile applications
There are more than 200 billion mobile app downloads a year, and both Android and iOS application collections are growing daily with more and more apps to choose from. However, as anyone with a cyber security degree can tell you, this stratospheric growth in app usage comes with a higher risk of cyber attacks and can make both your physical device and the data on it, much more vulnerable.
Before you go to delete your entire app library, however, there are several things you can do to help you decide whether or not a particular app poses a hazard. Many third-party apps, particularly those linked to reputable organizations or institutions, such as online banking apps or e-commerce apps, have been designed and checked carefully to ensure they operate safely, and that users’ data is not at risk of being leaked.
However, there are also several other apps that have been found to jeopardize users’ devices and data in various ways, for instance, through the addition of covert spyware or tracking software that may retain personal information or data entered through a mobile device’s keyboard. Before downloading a third-party app, it is always worth doing some comprehensive research into it first, by checking reviews and customer feedback to look for any potential issues that may be present.

Check your Wi-Fi
The great advantage of using a mobile device is that it is both incredibly portable, and you can get online with Wi-Fi networks available virtually everywhere. Mobile phones can be a handy tool to check your email, stream the latest music, watch a video or keep up to date with your cybersecurity degree, but there are some important things to keep in mind when using Wi-Fi services.
Public and free Wi-Fi is increasingly commonly found in most public areas, such as coffee shops, shopping malls, and other popular locations. Many of these may ask you to submit an email address or phone number before allowing access, but there are also several that will not require any input at all. While these can be useful for accessing general online data, such as checking a map application or accessing your messages, you should be wary of using any kind of secure application on your phone when using public Wi-Fi service. Unsecured Wi-Fi networks can allow other users to deliberately or inadvertently access your online activity, putting sensitive information, such as passwords, email data, and other information at risk of snooping.
To avoid any potential cybersecurity degree-level issues, steer clear of public and unsecured Wi-Fi services when you need to access any kind of password-protected or sensitive information on your mobile. You may also want to invest in a VPN, or virtual private network, which enables you to have a secure browsing experience, even when using an unsecured service. Alternatively, you may want to stick to your mobile data provision and avoid Wi-Fi away from home or work entirely.
Keep your software up to date
One of the key insights you may learn when taking a cybersecurity degree is that it is not only actively malicious acts that can put your online information at risk. As mobile and other digital forms of technology change so frequently, it’s easy to fall behind and find that your operating systems have become out of date.
You should avoid dismissing frequent software updates as a gimmick or annoyance. While they can certainly seem to be a pain to keep going through, they do serve an important purpose. Software updates are renewed so frequently as they address the latest bugs and security issues that may have been detected, and many of these updates will take into account the findings of graduates from a cybersecurity degree, who are best equipped to identify potential issues in the industry. They may have identified potential vulnerabilities in existing software that make it easier for hackers to get into users’ phones, or found improvements on previous solutions, to make your mobile phone safer and easier to use. They may also include anti-virus software, which may provide extra protection against malware and other digital dangers.
Updating your software is usually quite straightforward, and most mobile phones will have an option to allow the latest updates to be downloaded and added automatically. If you’re not sure, you can also check in your phone’s relevant app store, to find out what the latest version of the system software is. You will need to bear in mind that some older devices may not support the latest systems, so if you choose to use an older phone, you may have to compromise on the software system you’ll have access to.
Use a secure PIN or lock
The vast majority of contemporary smartphones will have some kind of security locking option available, ranging from traditional options such as numerical PINs or passwords to security patterns, fingerprints, and even retina recognition. There are advantages to each of these, and a cybersecurity degree is a useful way of building a knowledge of the complexities of the different security methodologies around at present, and it could be the key to a career in the industry.

Whichever access solution you choose, having some form of secure lock on your phone is essential, as it can prevent your mobile phone data from being accessed by a third party, if your phone falls into the wrong hands, for example. PINs and passwords do run the risk of being guessed, so you should be mindful not to use the same password for everything, and avoid noting down your phone’s passcode anywhere that is easy to find. Other forms of locks such as fingerprints or retina scans are highly individualized and provide a much greater level of security, as it is immensely difficult for someone to reproduce these things.
You may also find that your phone usage may be limited if you do not choose a security option. In many cases, secure applications, such as online banking apps, will require that the phone has a reasonable form of security enabled. Unless you do not intend to use the phone for any kind of sensitive information exchange, which is highly unlikely for most phone users, having a password is of paramount importance.
Anti-theft options
Losing your phone or having it stolen is a nightmare that has happened to many people. Fingers crossed that some boffins with a cybersecurity degree can come up with the perfect solution in the future. But in the meantime, many phone providers of both Android and iPhones will offer features that allow you to track your handset, and this can be hugely helpful in the event of a theft. These applications will often provide detailed and real-time information about where your phone may have been located and what has been used on it. By using these, you can often rule out whether a phone has simply been lost somewhere, or if it has actually been lost.
Alongside the ability to track and find your phone, these applications can also provide you with the option to reset your phone, back to factory settings. This will carry out a remote clean wipe of all of the data on your phone, making it impossible for anyone to access what you had on there. Although this means that it is impossible for you to recover what was on your phone too, it does keep your data safe from harm.
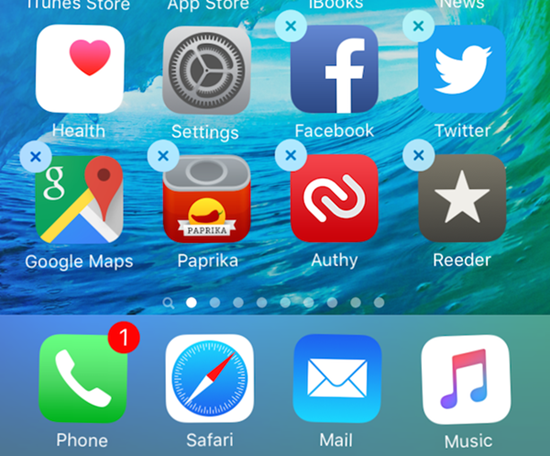
Delete any apps or services you no longer use
With the hundreds of apps on our mobile devices at any given time, it is easy to overlook the older ones lurking in the background and consign them to history. However, while they may be gathering digital dust, in reality, they can continue to pose a serious risk of danger to you, simply by being there. If you’re interested in finding out more, a cybersecurity degree will provide you with all the know-how.
There are a number of ways that out-dated apps can cause problems. You may have games you’ve gotten bored of, social network platforms you no longer use, or various other apps designed to perform some kind of rudimentary task. Keeping them on your phone will occupy valuable memory space and processing time, and can cause your phone to run slower, or have more frequent issues, particularly if you have severely overloaded the phone’s capacity.
Older apps, even when they are no longer in use, may also act as unwitting Trojan horses, exposing your phone and information on it to being accessed surreptitiously by hackers, or they may collect your data and pass it on to third parties for marketing purposes. Consequently, it is wise to carry out a regular purge of these apps once you have found that you no longer use them. Even if they are redundant, this does not prevent them from being used by others to cause major damage.
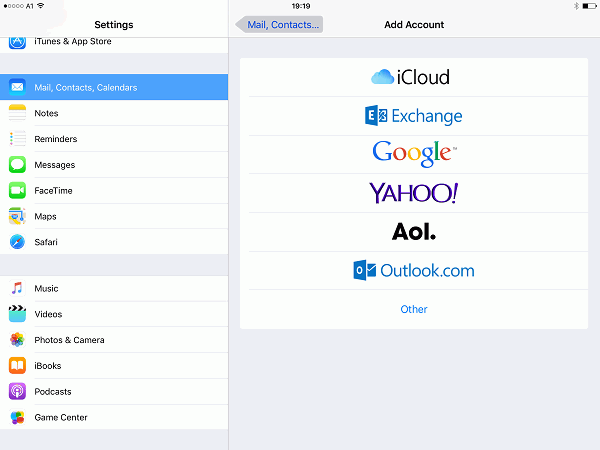
Manage your mobile wallet
With the emergence of mobile payment options, smartphones have increasingly become many people’s payment method of choice. There are several advantages of using your mobile phone to make payments: you can avoid having to carry around additional items such as a wallet, physical payment cards, or cash; and mobile payments can increasingly be used in a wide variety of places, from public transport to cafes, stores and more. And for anyone studying a cybersecurity degree, it might come as a surprise that mobile payments are potentially safer than using a credit or debit card.

One of the main reasons that a mobile payment method can provide additional security, is due to encryption, a subject that a comprehensive cyber security degree will address in detail. Rather than displaying your full credit card details, a mobile version of it will carry encrypted information, which is used to authorize and complete the transaction. No actual financial information is transferred across, and this makes it much more difficult for hackers to access your card or financial details. Conversely, if a credit card is stolen or cloned, thieves can often have direct access to your account, and may only be detected if an erroneous payment is flagged.
However, that doesn’t mean that all mobile payment options are entirely safe. One important factor to keep in mind is making sure that you use a trusted and verified app to add your payment details. Many banks offer this in addition to existing mobile banking apps, as well as other major online payment portals, such as Google Pay or PayPal. Be wary of using unknown third-party apps that may claim to offer easier or better access, as these may inadvertently expose your financial details to cyber criminals.
You should also pay close attention when making payments online through e-commerce platforms and other sites. A trusted site will have secure encryption to make sure that the transaction is protected throughout the process. In addition, most major card providers will request additional verification and authorization before completing the payment. In some cases, banks may even freeze your card and transaction until they have contacted you directly, to confirm it is a valid payment.
While mobile phones can present many potential security concerns, there are still several robust and well-designed solutions out there to help keep you safe when online.